The first vulnhub image I found was called Billu-b0x. Below is the link to the image on vulnhub that can be downloaded. This image has a variety of walkthrough exercises already, the one I have chosen to highlight and also follow closely is listed below.
Vulnhub Link: https://www.vulnhub.com/entry/billu-b0x,188/
Highlighted Walkthrough:
https://scriptkidd1e.wordpress.com/billu-b0x-vulnhubs-vm-walkthrough/
Tools Used:
VMware Workstation 12 Player
PuTTY or SSH client on host computer
Billu-b0x VM
Kali Linux Distro VM (Downloaded the VM edition from kali.org)
1 - nikto - Nikto Web Vulnerability Scanner
2 - dirb - Directory Buster
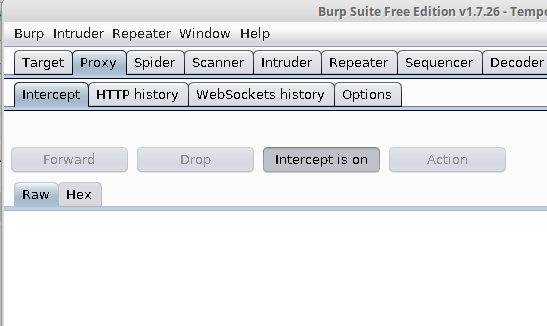
3 - burp - Burp Suite Free Edition v1.7
4 - Firefox Web Browser
1. Setup the Kali VM and the Billu-b0x VM with host-only network settings. Conduct both actions prior to powering on the VM. Both VM's require at least 5 GB of host memory to run in parallel. I would recommend that you run the VM's on an SSD drive.
2. Find the IP Address that was given to the Billu_b0x VM. The IP Address provided in my environment is 172.16.216.129. Then run a nmap scan on the IP Address to identify the open ports.
Command: nmap -sV 172.16.216.129
3. The port scan came up with 2 ports being open. Ports 22/tcp SSH and 80/tcp HTTP. A step that I would take is to google the versions of the tools displayed to identify any vulnerabilities that would be applicable. To keep this brief I am not going to include my results.
4. My host is running a version of Linux, this step is not necessary to the completion of the lab, but I am going to demonstrate how I am using SSH to utilize X11 forwarding so that Burp Suite and Firefox running on the Kali VM appears on the host screen. (There are tools to do this when the host is Windows, google it.)
Command: ssh -X root@172.16.216.130 (The -X option allows the X11 forwarding. Run the command 'man ssh' for additional information about this and other parameters that can be used)
5. If you ran the command for step 4 correctly, you should see a prompt indicating that you logged in correctly. The default root password for Kali is toor. Note: You will need to modify the SSH configuration on the Kali VM prior to step 4 working. To do this modify the file on the Kali box to appear as the following screenshot.
Command: vim /etc/ssh/sshd_config OR nano /etc/ssh/sshd_config (Google the commands to find a cheat sheet for them.)
Scroll down to verify the X11Forwarding is set to yes... On a production system you would probably set this to "No".
6. Now through the SSH session that is established I am going to launch firefox on the Kali box and it is going to appear on my host. Notice the heading of the window that pops up it shows '(on kali)'
Command: firefox
7. Using firefox I am now going to browse to the site and see what it presents.
URL: http://172.16.216.129
8. By reading the page you can quickly see that it provides a hint that there may be a sql injection vulnerability. However, prior to jumping to finding a sql injection vulnerability, look around more. Right-Click on the page and View the Source Code. Sometimes you can find additional information, pages, or hints to what you need to do next. Check to see if a robots.txt file exists, http://172.16.216.129/robots.txt. Google what the purpose of the robots.txt file is if you do not know.
9. I like a tool called nikto. It is a web vulnerability scanner that I typically execute when I first come across a page.
Command: nikto -h 172.16.216.129
10. Again, do not jump to fast into testing the vulnerabilities, continue to gather information about the virtual machine. Record the results of what you found with the nikto command. We will come back to it.
11. Now we are going to use dirb or directory buster. This will brute-force the URL and try and find additional pages or directories that we currently do not know about. We are going to SSH into the Kali VM, you can utilize the -X command line switch as demonstrated above. You will have multiple SSH sessions open by the end of this.
Command: dirb http://172.16.216.129
Command: dirb http://172.16.216.129 /usr/share/wordlists/dirb/big.txt
12. In the above output from dirb you can see a couple more directories were found. As you read the individual lines the code is the HTTP code that is returned, 200 for a successful page load, a 302 for access is denied, etc. Google the HTML Codes if you have more questions.
13. With the information gathered start to visit the pages and gather more information of what the pages can do, what language the pages are written in, etc. Try not to focus again on any particular page, just look through them.
14. Also knowing that it found PHPMyAdmin located under the directory of http://172.16.216.129/phpmy/ I reran nikto with this information to find some additional vulnerabilities. Note: PHPMyAdmin normally has vulnerabilities and exploits published about it.
Command: nikto -h http://172.16.216.129/phpmy/
15. Notice as you browse these files that are found, you find a README file that shows the version of PHPMyAdmin being 3.4.7. A quick google search identifies an exploit that is published that allows an authenticated attacker to inject an XML file and read arbitrary files like /etc/passwd.
16. After going through the files I am going to go back to the file http://172.16.216.129/test.php. I am intrigued by the message presented on the page. Maybe the file parameter can be used to read files on the web server.
17. To work more with the 'file' parameter we are going to use the Burp Proxy that is on the Kali server and X11 forward the GUI portion of the tool like we did for firefox above. After it loads leave it as a temporary project and then click next, load defaults and then click start burp.
Command: burpsuite
18. After burp loads, we need to turn the interception off. Click on the "Proxy" tab and then click on "Intercept is on" and it should say off after clicked.
19. This setting is not necessary but I am demonstrating how it is done in the event you need to use it. Under the proxy tab click on options. Notice that the proxy is only listening on localhost port 8080. If you have multiple people utilizing the proxy or a local browser using the remote kali proxy you need to edit the setting and change it to all interfaces. After you click ok, it will restart the listening port to be on all interfaces utilizing port 8080.
20. Now to allow your web browser to proxy the page your are visiting you need to configure the browser to use the burp proxy. Below is a screen shot of how to get to the settings and then how I have configured them. I am utilizing Firefox.
21. Now when the page http://172.16.216.129/test.php is hit through the browser, it should show up in burp under the tab target. Now right-click on the test.php and then in the menu click on "Send to Repeater". The tab should change colors.
22. When you click on the repeater tab you should see the below image. Remember that a web request is only text that is interpreted by the web server, in the case of PHP it is server-side.
23. Change the request being sent to the web server to be a POST and then add a parameter of "file=/etc/passwd" as shown below.
24. Notice that the response that is returned has the same message, file parameter is empty. You need to work with the request headers and add the Content-Type header listed below. Work with it until the response comes back with the contents of what appears to be the /etc/passwd file.
25. Now that we can display the contents of a file on the file system, let's look at the PHP code in the files that we know about. Notice in the c.php file that we found using dirb contains a username and a password that connects to a mysql database.
26. Now that we have a username and password we can use this to login to PHPMyAdmin. PHPMyAdmin is used to manage the database using the particular users rights. After logging in you can see the tables you have access to and more...
27. In PHPMyAdmin click on Databases, then underneath database select ica_lab.
28. Then click on the auth table.
29. Now you can see under options the values of the database with it showing a plain-text password for biLLu. This use can be used to now login to the page at index.php.
30. After successfully logging in you can see the below screenshot.
31. To keep this brief, I am going to jump back to the vulnerability that you can utilize to view the source code of a file. We are going to look at the configuration file for PHPMyAdmin. This file is located normally at the root of the PMPMyAdmin installation. For this site the file is located at http://172.16.216.129/phpmy/config.inc.php
32. As you look at the file that is returned you notice that the PHPMyAdmin software is configured with the root username and password. Because of password reuse on systems you can use this username and password combination to login as the root user through SSH.
This walkthrough I am going to conclude, however there will be more to come. Take time to explore other ways to exploit this VM.
Enjoy.